Customer Data Protection
In previous articles we’ve covered the collection of customer data from various sources, choices in storing the collected data, and which platforms to use for gaining insights and forecasting. In this article, we’ll look at customer data protection.
Once collected, customer data — especially the personally-identifiable information (PII) that ties data to a particular person — is both a company’s most valuable crown jewels and also, potentially, its greatest vulnerability. The bad press and resulting loss of consumer trust that comes from losing PII through a data breach can be catastrophic for a company. The same goes for regulatory fines levied due to improper handling of PII. Undeniably, the decision to collect PII comes with consequences.
If you are working with customer data, like you might in a customer data platform you must mitigate these liabilities with a customer data protection plan.
Understanding the lay of the land
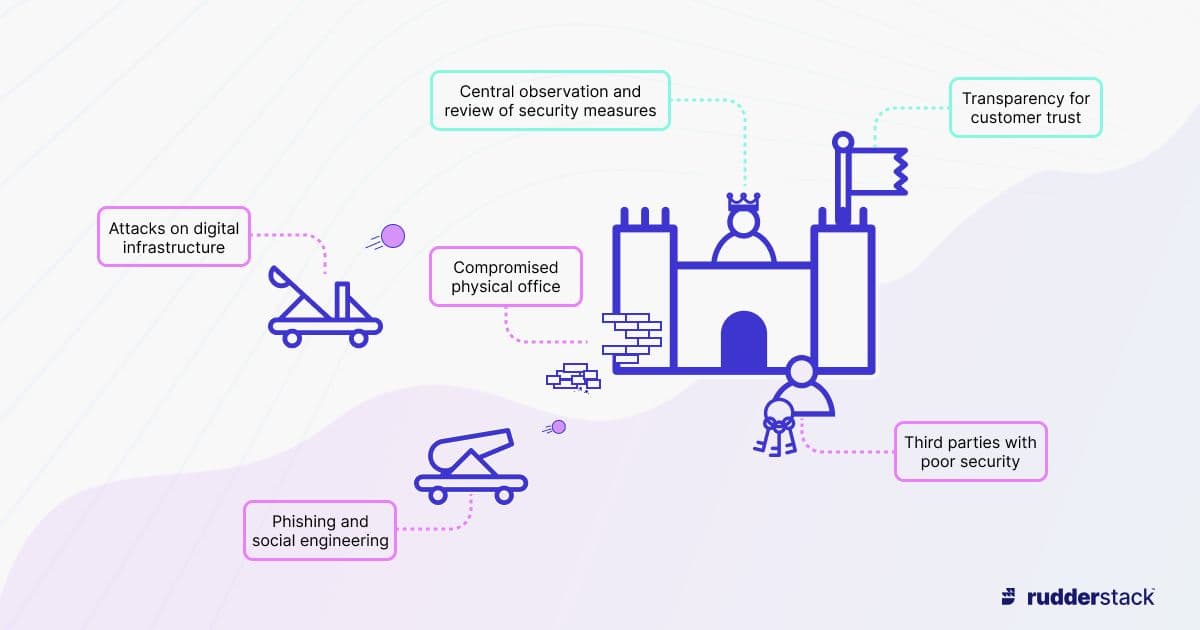
In the language of computer security experts, you must accurately assess the attack surface area presented by your business, through exposure of both digital and organizational infrastructure, as well as the lure of your customer data. Understanding the security environment surrounding your valuable data is the first step in protecting it.
The physical and the virtual
When we think of data security it’s usually the virtual data forms that come to mind. But vulnerable data also exists on your servers, laptops, mobile devices, and local storage like thumb drives, and in printed form.
All these attack surfaces must be locked down to ensure complete protection. Office security is essential: protect each facility and sensitive areas within them using key card access control, use video surveillance, and secure physical data behind locks. There is a saying in IT security: Once someone has physical access to the device, it is only a matter of time before they can access the data contained. That is why you must deploy a robust IT management system to counter laptop and mobile theft and loss, and implement a process for destroying retired physical data stores.
The discussion of physical security may seem inconvenient or even needlessly alarmist. But nearly every office space that hasn’t dedicated resources to the problem is easily penetrated, even without high-skill techniques, like lockpicking.
Take your partners into account
Your data security policy must take into account all of the places where your data goes in the normal course of business operations. Your customer data security must be matched by every third party with whom you share data.
Your website hosting service, cloud-based data storage, customer relationship management software, and off-site data backup services must all be evaluated. If one of them allows your data to be breached, the consequences — mitigation costs and fines, bad press, and loss of trust — will be yours.
Risk profile
Small businesses generally have less value to attackers, due to both the quantity of data collected and the number of customers. Their risk profile is therefore less than those of larger, big-name companies.
You need to find a balance between free, easy, access and costly, inconvenient, restrictive cybersecurity and privacy controls. Overestimating the sensitivity of your data or minimizing the negatives of breaches and regulatory fees will lead to an imbalance. Consider the results of bankrupting yourself on overly expensive security, making the data inaccessible with overly restrictive policies, or leaving yourself vulnerable by doing too little.
Estimate your risk profile and use the collected wisdom of data security professionals to come up with a workable solution for your particular situation.
Protecting customer data demands awareness and competence on many fronts.
Monitoring, testing, and compliance
Monitor the state and location of your data storage, and evaluate the extent of present threats and related security efforts (like firewalls) on an ongoing basis.
Regularly test your cybersecurity systems through spot checks and full-blown “red team” attacks. This exercises existing security efforts, provides practice in shutting down systems under attack, and tests the forensic response to find the vulnerability and identify attackers. It also provides a feedback mechanism to shore up defenses and protect data.
Assign dedicated staff to understanding and complying with applicable data protection, such as the General Data Protection Regulation (GDPR). Ensure they keep up to date with the practical requirements of data retention policies and legal discovery mitigation on an ongoing basis. This is also essential to your overall security profile.
A very basic set of test for cybersecurity are:
- Trying to access data that should require authentication, while not being authenticated. For example, can you get to the Edit page of an article in your CMS while not logged in?
- Trying to access data that requires not just authentication but authorization as well. For example if your user ID is 123 and the URL to edit your user profile is `/users/123/edit`, can you change and save information on `/users/456/edit`?
Transparency
Open communication with customers and third parties after detecting a data breach is just as important as implementing the security plan. Having a what-if plan of ways to transparently share information and efforts inside and outside your organization in a timely manner is critical and must not be overlooked. There’s a huge difference in the damage to a company’s reputation when they report breaches quickly, like this American Airlines breach that was publicized within a week, vs. Equifax who took over two months to report a breach.
Protecting customer data
The following are some industry best practices for how to protect and secure customer data.
Eliminate the threat by transforming the PII
Above all other protective measures, consider the needs of data consumers within your organization for PII. Does each application, platform, and tool actually require the data to have PII attributes? Would your needs be just as well served by abstracting away the PII with some scheme of universal IDs? Perhaps anonymizing the data or encrypting the PII portion would serve just as well. Reduce your risk profile by making your target data useless to others. An example of this is why you often only see a credit card’s last four digits, as opposed to the full card number.
Know what, why, where, and when
Part of collecting data is identifying the sources. Vet your needs and trim what you keep to the minimum. Know what you’re keeping and why.
Know where the collected data is stored. Is there a central source of truth or is your data replicated during a flow from a lake to a warehouse? Is the data stored on premises, or in the cloud? Does it stay under your control or is it shared with third parties? Do they need the data in PII form? Is your data encrypted both in transit AND at rest?
Know when to prune your data. Determine what is valuable history and what’s clutter. Can historical data be stripped of PII?
Secure the whole system
Map the entire data flow and ensure you’ve secured each step of the process.
Make a plan for mobile, laptop, and desktop security for theft, loss, and retirement. Add access control to your networks, WiFi access points, access method (prefer WPA2, and consider MAC address whitelisting or restricted guest networks for visitors to your workplace), and password requirements. Consider expiring passwords on a balanced schedule that doesn’t frustrate users — or they may resort to leaving password reminders in plaintext. Add multi-factor authentication that does not rely on insecure SMS, and a managed device policy. Require all external network access to use a virtual private network (VPN) with revocable access. Ensure everything that has a firewall has proper access and denial rules.
Deploy anti-malware, anti-virus, and anti-spyware solutions as appropriate. Filter email to quarantine those with viruses and phishing attacks. Ultimately encrypt everything, from laptop drives to server storage and backups.
Centralize responsibility
The best-laid plans will fail without at least one person responsible for data security, regulatory compliance, and legal and discovery enforcement. Their salary is certainly less expensive than the costs associated with breached PII and running afoul of regulatory demands.
Employee education about cybersecurity and the security testing procedures requires someone who cares about them being carried out and about the results.
The security manager may also be the person who keeps up with regulatory decrees. Familiarity with demands based on your geographic and geopolitical location, as well as demands based upon the kinds of data stored (such as GDPR for PII, or the Payment Card Industry Data Security Standard (PCI DSS) for credit card information), will focus your efforts.
MARCOM must communicate bad news, as well as good
Your marketing communications staff should have plans in place to react to data breaches. Timely and transparent communications will make the difference between your efforts being seen as commendable or as a cover-up. Your reputation will be at stake, and any breach will eventually make it into the public sphere — being ahead of the news will allow you to frame how the response is perceived.
Iterate and improve your security — and use the right data tools
All of the above efforts must be repeated frequently enough to be able to assess the current threat picture and form and deploy plans to protect your customer data.
A security checkup is not a one-off task: you must monitor your data infrastructure continuously for potential attack vectors. Allowing security protocols and measures to atrophy – and especially allowing complacency to creep in – is a guaranteed way to leave yourself open to a customer data breach. Likewise, leaving production systems unsecured - be it without firewalls or unrestricted permissions, or default credentials that make testing and development easier - is one of the first things an intruder will look for.
Further Reading
Before beginning your customer data protection campaign, it is worth refreshing your knowledge of core data concepts and system patterns. Other articles in our series that you may find helpful include: