Blog
Managing Permissions in a Complex Data Ecosystem
Managing Permissions in a Complex Data Ecosystem
Brian Lu
Director of Product
3 min read
July 19, 2022

Data systems are more complex than ever. It’s getting harder to ensure that the right people have the right access to do their jobs effectively. On one side of the balancing act is the need for velocity and data democratization. On the other side is the increasing importance of reliability, data privacy, and data security.
When it comes down to it, permissions management is an exercise in precision. If your permissions are too loose, there is an increased risk of data breaches, broken pipelines, and privacy regulation non-compliance. If your permissions are too tight, it becomes difficult for data users to run analyses needed to make decisions, create informed marketing campaigns, and gather the context for effective customer conversations.
To help you overcome these challenges, we’ve added two key features that enable you to fine tune user permissions. With these features you can:
- Lock down business critical pipelines
- Limit access to debugging features where raw data is exposed to ensure data privacy
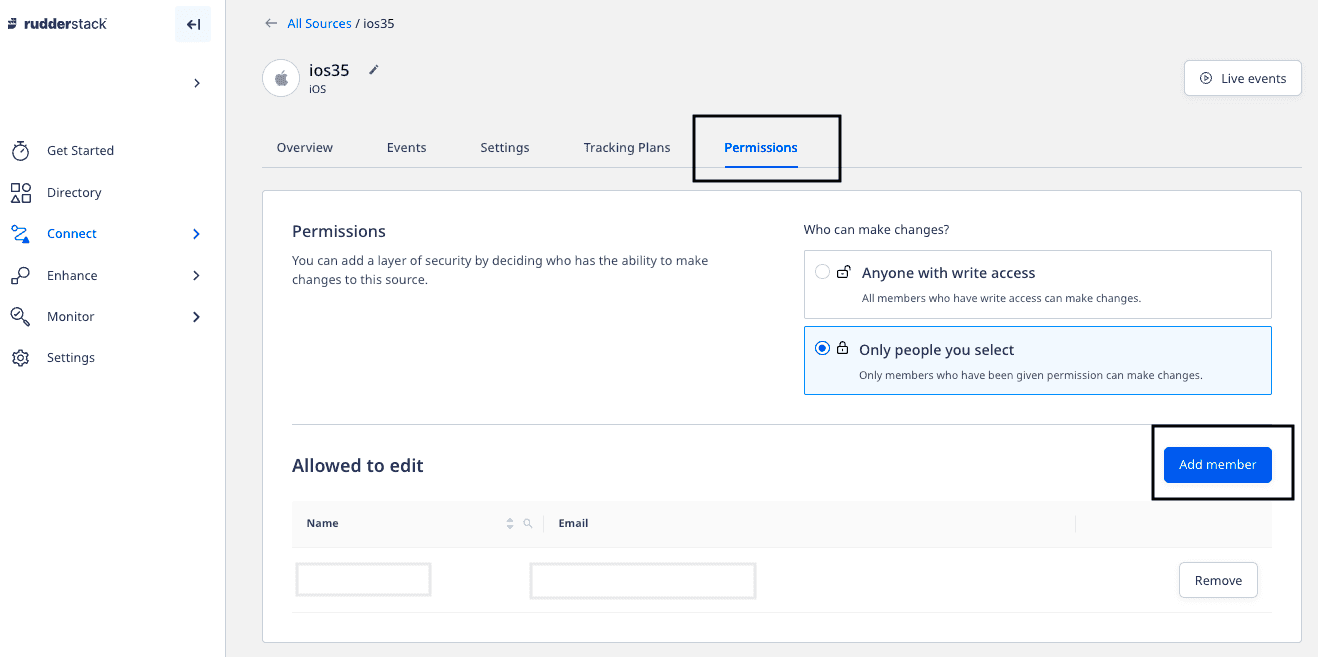
Locking down business critical pipelines
Administrators can now lock down any source or destination. When you put a source in lockdown mode, only a specific list of people will be allowed to update the pipeline. No new connections can be added to locked down objects.
When you lock down a destination, we want to give you peace of mind that the ground will not shift under your feet unexpectedly. When issues do happen, you can easily work on fixing pipeline errors with the people who you’ve trusted with access.
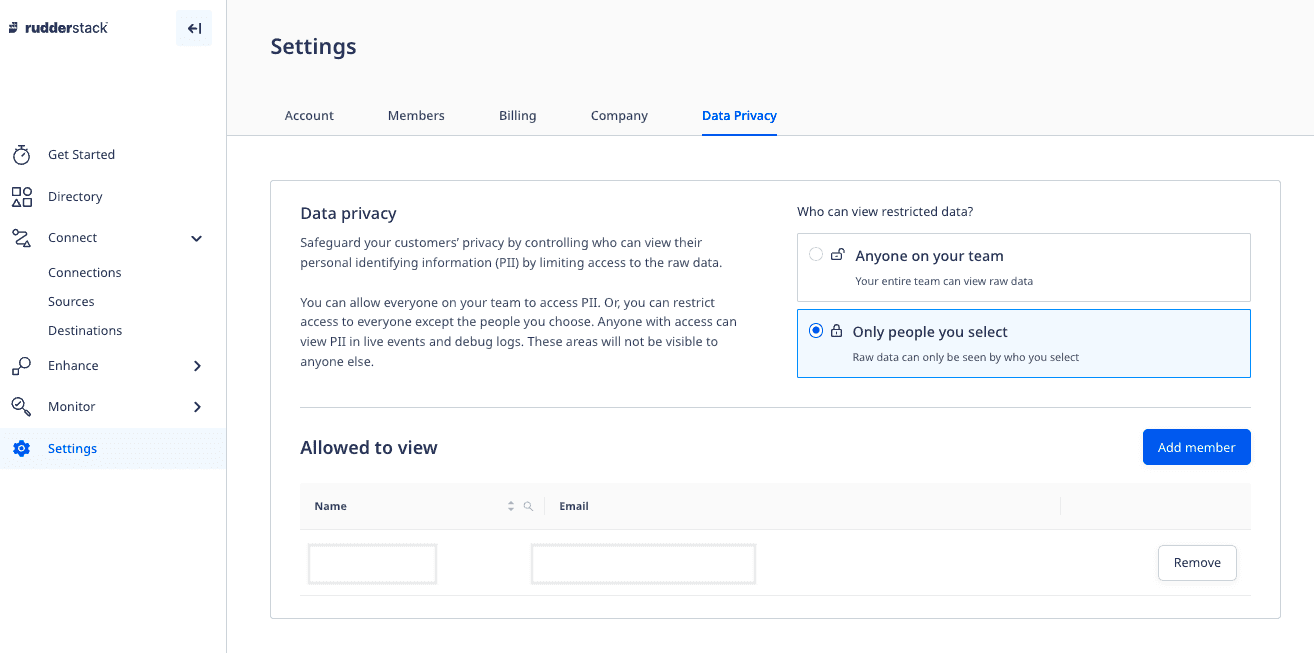
Limiting access to debugging features where raw data is exposed
Some important debugging features in RudderStack, such as Live Events and Destination Failures, include raw data payloads. Depending on how you are using RudderStack, these payloads may include PII (Personally Identifiable Information) or other data sensitive to the organization.
Our new Data Privacy section allows you to configure who can use features that expose raw data to individual users. This enables you to provide collaborators within RudderStack the ability to update and maintain pipelines without any risk of exposing PII to your users.
Note: RudderStack does not store any of your data permanently. It only holds your data in transient storage for these debugging features.
Additional Improvements
In addition to these new features, we have made visual updates to our Teammates page and updated permissions documentation with details on our role-based access permissions.
Neither individuals or tooling can solve permissioning challenges on their own, but with the right combination you can create a program that works for your organization. At RudderStack we want to help you get one step closer to both empowering your data users and having a well-defined risk profile for data privacy, security, and operations.
Check out the video below for a five-minute walkthrough of these new features:
- Permissions Management Doc - https://www.rudderstack.com/docs/dashboard-guides/permissions-management/
- How to Add Users + User Permissions - https://www.loom.com/share/232d08f904774fb18c79dde41313b316*
Published:
July 19, 2022
More blog posts
Explore all blog posts
How to improve data quality: 10 best practices for 2026
Danika Rockett
by Danika Rockett
AI is a stress test: How the modern data stack breaks under pressure
Brooks Patterson
by Brooks Patterson

Generative AI risks and how to approach LLM risk management
Danika Rockett
by Danika Rockett
Start delivering business value faster
Implement RudderStack and start driving measurable business results in less than 90 days.